New domain name for my blog
It’s been over a decade since I emigrated from the UK so I thought it was time I update my domain name to be more international.
Migrating to Github Pages
Today I Learnt that deploying a jekyll site (the tool used to build this website), is relatively simple.
Simple instructions are availble on the github site and this site is now live.
pfSense log parsing in Graylog (including suricata/snort)
This guide is the second part in a series which looks at setting up a grafana dashboard for your pfSense network, the first part should be completed before following these steps.
pfSense log consolidation to Graylog (including suricata/snort)
This guide is an overview of how to push logs from pfSense (an Open Source firewall) into Graylog (an Open Source log aggregated and parser).
Site Cookies
Yes our site uses cookies, it’s just to provide website stats with Google Analytics as I’m a data junkie. If you’re uncomfortable with that then you don’t need to accept them and the site will continue to work.
What does your Smart City look like?
As our World becomes more connected with every passing second, what will our Smart Cities become as they start to work to be better, safer places for us?
Council’s focus currently on optimising their existing services, but what would you do if you could design your ultimate Smart City? Discuss.
To Be a Tech Leader, Kill the Tech Talk
When I moved from startups to big business I used to get frustrated that my technical know-how wasn’t immediately understood and valued — what was the point of having to explain myself when we could just be getting on with work?
5 Ways to Stay Strategic on Your Way to the C-Suite
I remember they day it happened. At first all I felt was shame and disappointment; it was the day my software developers said to me, “We’re not letting you write code anymore.”
Don’t be an idiot — encapsulate unique business knowledge in your digital twins
For me the title says it all but if you still need to be convinced, first of all catch up on Eight Ways Digital Twins Can Action Real Change and Why you need to invest in heroes to build Digital Twins, then read on.
Why you need to invest in heroes to build Digital Twins
Successful Digital Twins should be enablers within your organisation, increasing safety/productivity and encapsulating unique business knowledge.
5 Ways Digital Twins Can Action Real Change
In the buzzword heavy industry that is technology Digital Twins have reached unicorn status; used within organisations and dropped into conversations to show street cred and innovation in an era laden with version numbers: Industry 4.0, Digital 4.0, etc.
2 tips to avoid Siri’s fate in your digital transformation
I’ve spoken previously about a passion to be the best and why it is important to set big hairy, audacious goals when it comes to digital teams and measuring success.
3 Keys to Successful Digital Transformation
The knowledge data brings is a key foundation to Digital Transformation, Industry 4.0/X.0.
Work on a shire horse not a unicorn startup
Life is too short to spend time on something you don’t love so concentrate on making your startup a shire horse, not a unicorn (although you might get that too!).
10 reasons an Enterprise Architect is like being a new parent
I have been a first time father for almost 3 weeks. Whilst chatting to one of my mates we had a laugh about some of the similarities between parenthood and being an EA:
10 things you need to do as a Vanguard Enterprise Architect
As Enterprise Architecture matures two roles are emerging — foundational and vanguard. If you’re looking to focus on the later, here are my top 10 focus points.
Why you must use Open Source at your Enterprise
It’s November 1989 and Tim Berners Lee has just viewed the first ever web page on the system he invented. He has two choices - turn it into a proprietary system and sell it, or give it away as an open standard. Had he chosen the former we may not have the likes of Amazon, Netflix or iPhone to enhance our life.
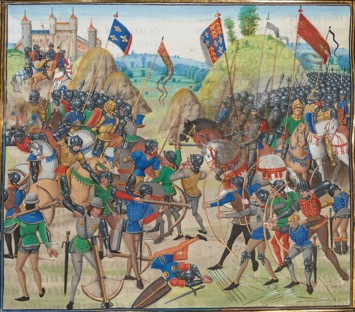
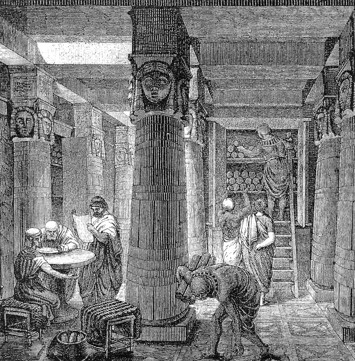
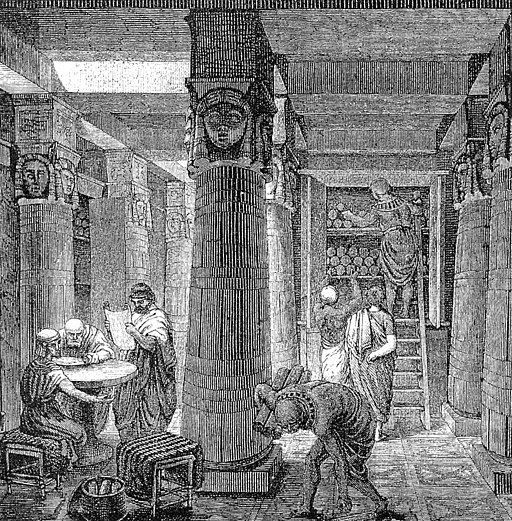
DynamoDB Outage, The Library of Alexandria and BCP
The Library of Alexandria was one of the largest and most significant libraries of the ancient world until its destruction in 48BC (or maybe AD 270 – 275, AD 391 or AD 642).